9 April 2026 - Research
We analyzed a 2025 sample of the Spyrtacus spyware, version 8.71. Among its capabilities it can record the screen and take screenshots, record voice calls, export WhatsApp messages, upload files, and dynamically execute downloaded modules. We confirm attribution to SIO S.p.A. and provide a small set of IoCs to detect infections of this malware family.
As like the majority of low-cost spyware, infection starts by receiving an SMS instructing the victim to install a carrier‑provided app to keep their mobile service working. The SMS contains a tinyurl.com shortened link, which, after a series of redirects, points to a phishing page that mimics the victim’s mobile provider website. The threat actor maintains pre‑made pages for all major Italian carriers.
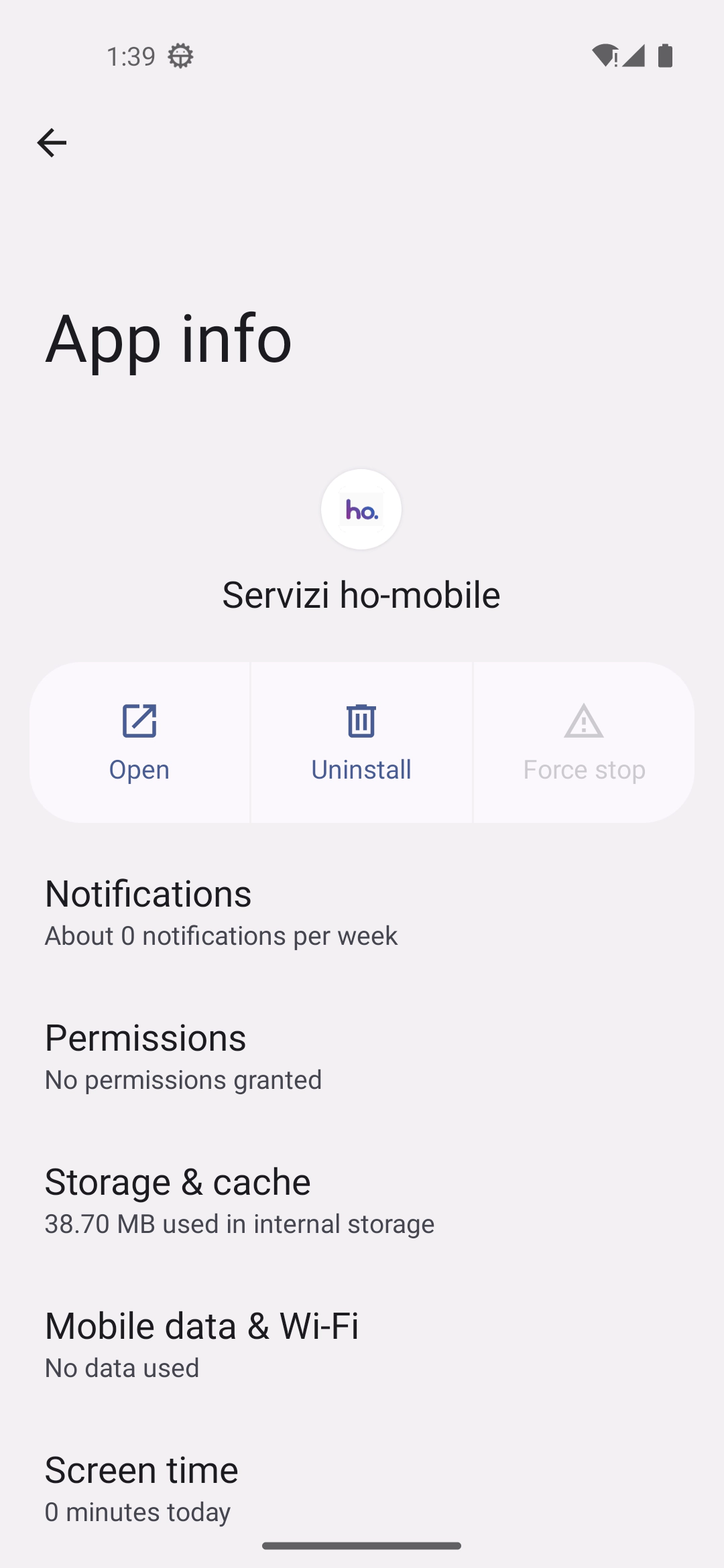
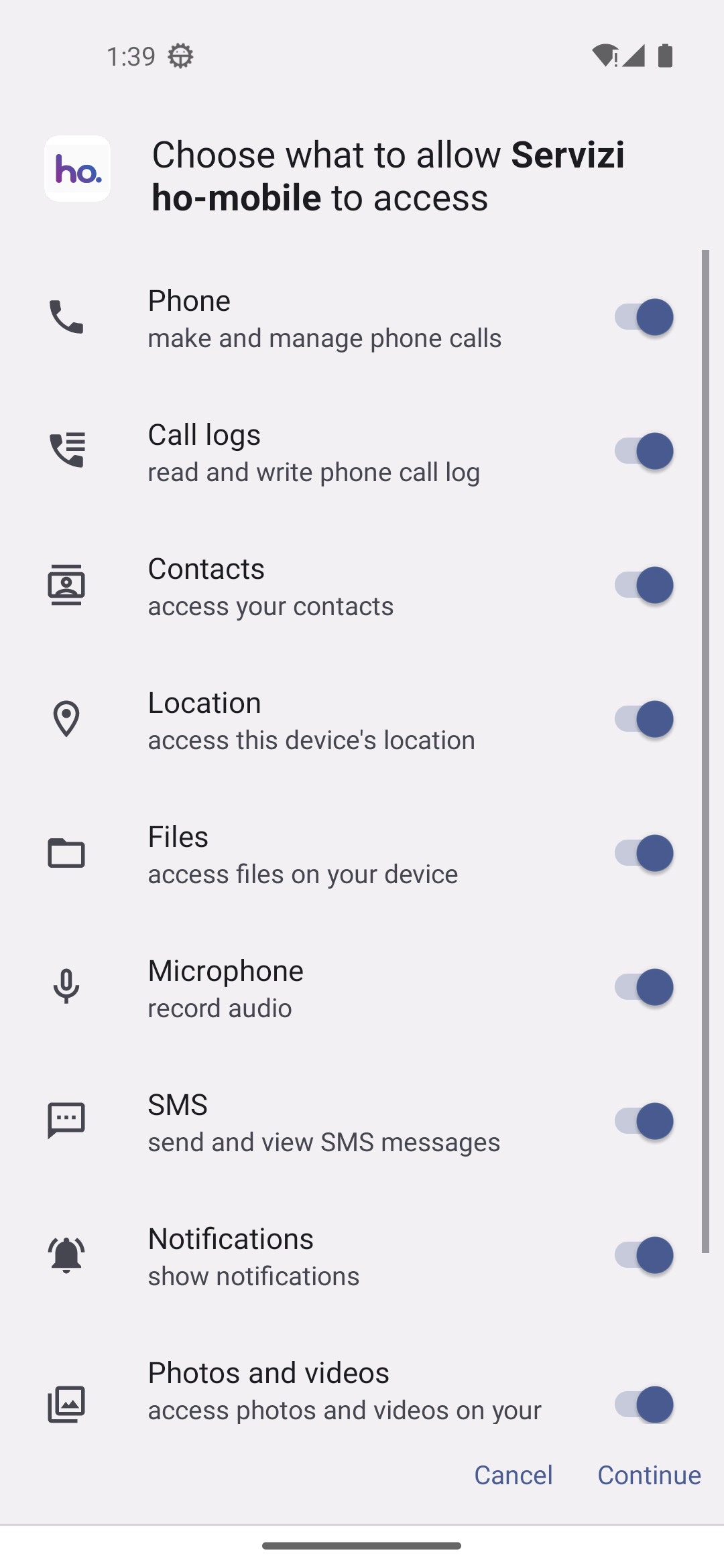
In this case the URL displays a page that imitates ho. mobile (ho‑mobile.it) and offers a download link to the malicious APK.
The application itself pretends to be the ho. mobile official app, advertising a new 5G promo. This tactic is common among low‑cost spyware families that rely on coercing users into installing malicious apps rather than employing sophisticated exploit chains.
In our case the application used the package name com.elysium.core, while its main activity was named it.taog.app.MainActivity. The application manifest reports versionCode="871" and versionName="8.71".
The app is signed with a key belonging to:
CN=Aziz Oukil, OU=Unknown, O=Unknown, L=Sant'Anastasia, ST=NApoli, C=IT
It is obfuscated with DexGuard 9.x. However, a string containing spyrtacus-agent can be found in the resources.
The Spyrtacus name is not new; this sample is likely a newer variant of the well‑known agent used by SIO.
During its first run the malware gathers device information, including IMEIs, and sends everything to a Dispatcher server via the /Dispatcher/GetParams endpoint. If no errors occur, the Dispatcher returns a set of parameters that enable or disable the spyware’s features.
Some of the parameters control whether the malware:
The malware can also download additional remote modules. The modules are AES‑encrypted DEX files that are loaded from memory through Android’s InMemoryDexClassLoader. The key to decrypt the modules is retrieved along with other parameters from the Dispatcher.
It is worth noting that in our sandboxed analysis we kept our sample offline, so we could not retrieve any of the module payloads.
During the onboarding process the Dispatcher server also returns the IP address of a Command‑and‑Control (C2) server that the agent will use thereafter. The C2 is then reached via a multitude of protocols including FTP, MQTT(S), HTTP(S), and Google’s Firebase services.
To validate the server’s certificate, the agent loads a key store embedded in the res/raw/ks file. The key store contains the following Issuer line:
C=IT, CN=Artemide/Spartacus, L=Roma, O=Coliseum, ST=Unknown, OU=Lotta Greco‑Romana
The same certificate is being served from an IP address belonging to AS206173 (an ISP named “NAVIGAZIONE INTERNET”, i.e., “Internet Connectivity”). This ASN is registered to SIOPLUS S.R.L. (VAT ID 10253360969), a subsidiary of SIO S.p.A..
To further confirm the attribution, we downloaded the favicon of one of the C2 servers.
The C2 favicon:

And the favicon from asigint[.]it, another SIO subsidiary:
As we anticipated, the application uses Google’s Firebase services, which is common for most Android apps because Firebase is ubiquitous on the platform.
In the context of spyware, however, this is noteworthy since it leaks to Google the correlation between spyware infection and the victims’ Google identity.
The following are the Firebase projects used by Spyrtacus:
https://assist-online.firebaseio.com
https://dusty-apricot.firebasestorage.app
To further corroborate the attribution, and in line with what TechCrunch previously reported about the Neapolitan dialect found in the spyware’s comments, we uncovered the following strings in the binary:
LA CODA INVIO E' VUOTA -- STATT BBUONPARAMETRI CONNESSIONE RICEVUTI -- SCATENATE L'INFERNO!These strings reflect the developers’ native‑language comments and further tie the sample to the known SIO‑related code base.
In the past other Spyrtacus samples were analyzed, in particular see the following list:
Version 8.65 from October 2024
Version 8.20 from April 2022
Version unknown from 2019
Apparently, a newer version of the spyware agent 8.72 exists, as documented: https://www.lawfulinterceptionacademy.eu/clir/.
IPs:
5.56.12.15089.46.67.218Domains:
supporto-mobile.itsrv.servicemnt.comAndroid package names:
com.elysium.coreit.taogorg.util.carriersvcsys.base.serviceC2 favicon SHA256 hash:
ef2e1c47166fe0c5ab3bf5216baf6ad6b96f759e15ac218d1a1a3cdcc9e0994fAs previously stated, and as supported by many NGOs, mercenary spyware should simply not exist. We reiterate the call to ban these tools and hold their operators and developers accountable, and we continuously advocate for that through our contributions and participation in the EDRi network.
You’ve read an article from the Research section, where we share the results of our technical and social investigations into networks, security, and surveillance, with the goal of deep understanding and public knowledge creation.
We are a non-profit organization run entirely by volunteers. If you value our work, you can support us with a donation: we accept financial contributions, as well as hardware and bandwidth to help sustain our activities. To learn how to support us, visit the donation page.